Digital identity on blockchain presents a policy-driven model where individuals own cryptographic keys and verifiable credentials anchored to ledgers. It emphasizes privacy by design, standards alignment, and risk-aware governance to ensure auditability and interoperability. Verifiability, consent, and revocation are core controls, with governance structures required for accountability and cross-border trust. The approach invites scrutiny of scalability, privacy trade-offs, and regulatory compliance, leaving open questions about implementation, oversight, and long-term trust sustainability.
How Self-Sovereign Identity Works on Blockchain
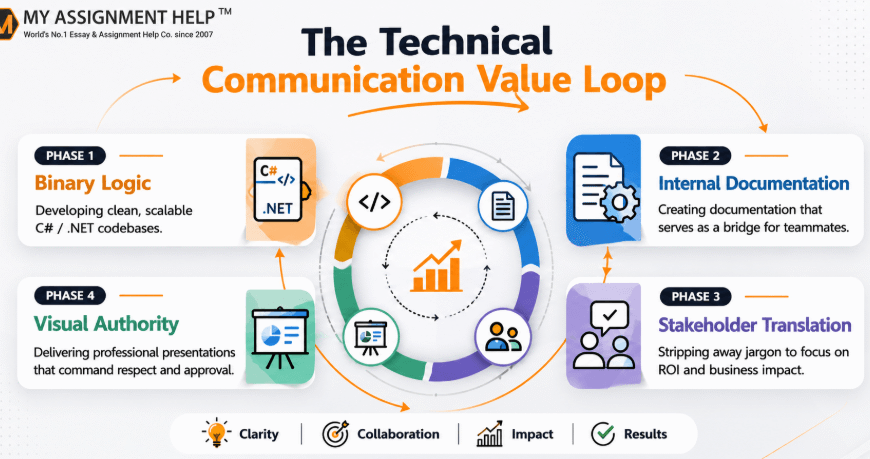
Self-Sovereign Identity (SSI) on blockchain empowers individuals to manage their own digital credentials without centralized custodians. The mechanism relies on user-controlled keys, decentralized ledgers, and attestations issued by trusted parties, anchored to standards for interoperability.
Risk-aware design emphasizes privacy by design and minimal data exposure, while decentralized governance sustains governance processes, audits, and accountability across diverse ecosystems.
Verifiable Credentials: Trusted Proofs You Own
Verifiable credentials provide trusted proofs that a digital identity possesses certain attributes or rights without revealing unnecessary data. They enable policy-aware governance of claims, balancing risk with user autonomy. Standards-driven approaches support interoperable issuance and verification, reducing friction for stakeholders. Credential verification processes safeguard integrity, while identity portability empowers individuals to move credentials across ecosystems without credential sprawl or vendor lock-in.
Building Privacy by Design in Digital Identity
Building Privacy by Design in Digital Identity requires embedding privacy considerations into every phase of identity systems, from inception through deployment and governance. The approach emphasizes policy alignment, risk assessment, and standards conformance to minimize data exposure. Privacy by design integrates governance and accountability, while data minimization limits collected attributes, reducing risk and enhancing user freedom without compromising verifiable functionality.
Real-World Use Cases and Adoption Pathways
Real-world use cases for blockchain-based digital identity demonstrate how policy, risk, and standards considerations translate into actionable deployments across sectors, from financial services to public administration.
Adoption pathways reveal scalable governance, interoperable schemas, and risk controls guiding implementation.
Sparse onboarding strategies reduce friction, while cross border adoption hinges on harmonized verifications, trusted custodians, and robust consent mechanisms for sovereign data stewardship.
See also: Technology and the Future of Education
Conclusion
In this evolving ecosystem, governance, granularity, and governance again guide growth. Privacy-preserving proofs, paired with principled policy, propel responsible, regulator-ready progress. Standards-driven stewardship sustains secure sovereignty, shielding sensitive data while enabling auditable attestations. Risk-aware frameworks foster interoperable integrity, ensuring identities remain portable yet protected across borders. With robust governance, transparent risk management, and accountable oversight, digital identity on blockchain advances trust, enables verifiable credentials, and supports prudent, policy-aligned pathways to widespread, sustainable adoption.